Workday - How do I link my account with an Integration System User (ISU)?
Last updated: October 30, 2025
Overview
To authenticate your Workday account, you will need to provide the following information:
WSDL
ISU Username
ISU Password
Workday Tenant Name
Prerequisites
Please ensure you fulfill all the requirements to set up the integration:
You have Administrator permissions in your company's Workday instance
Video Guide
This video outlines the setup process for an HRIS integration. The same steps can be followed for an ATS integration. The permissions in the creation of the configuration of the domain security policy (step 3 below) is the only difference.
Instructions
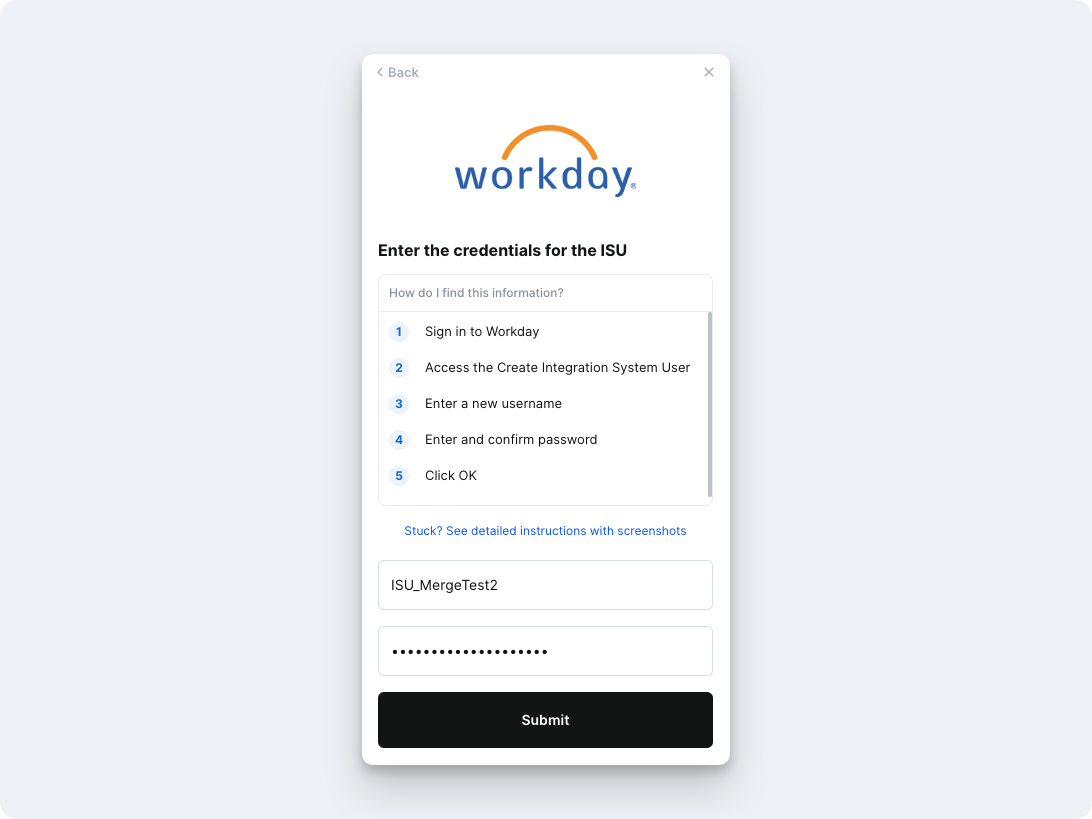
Step 1: Create an Integration System User (ISU)
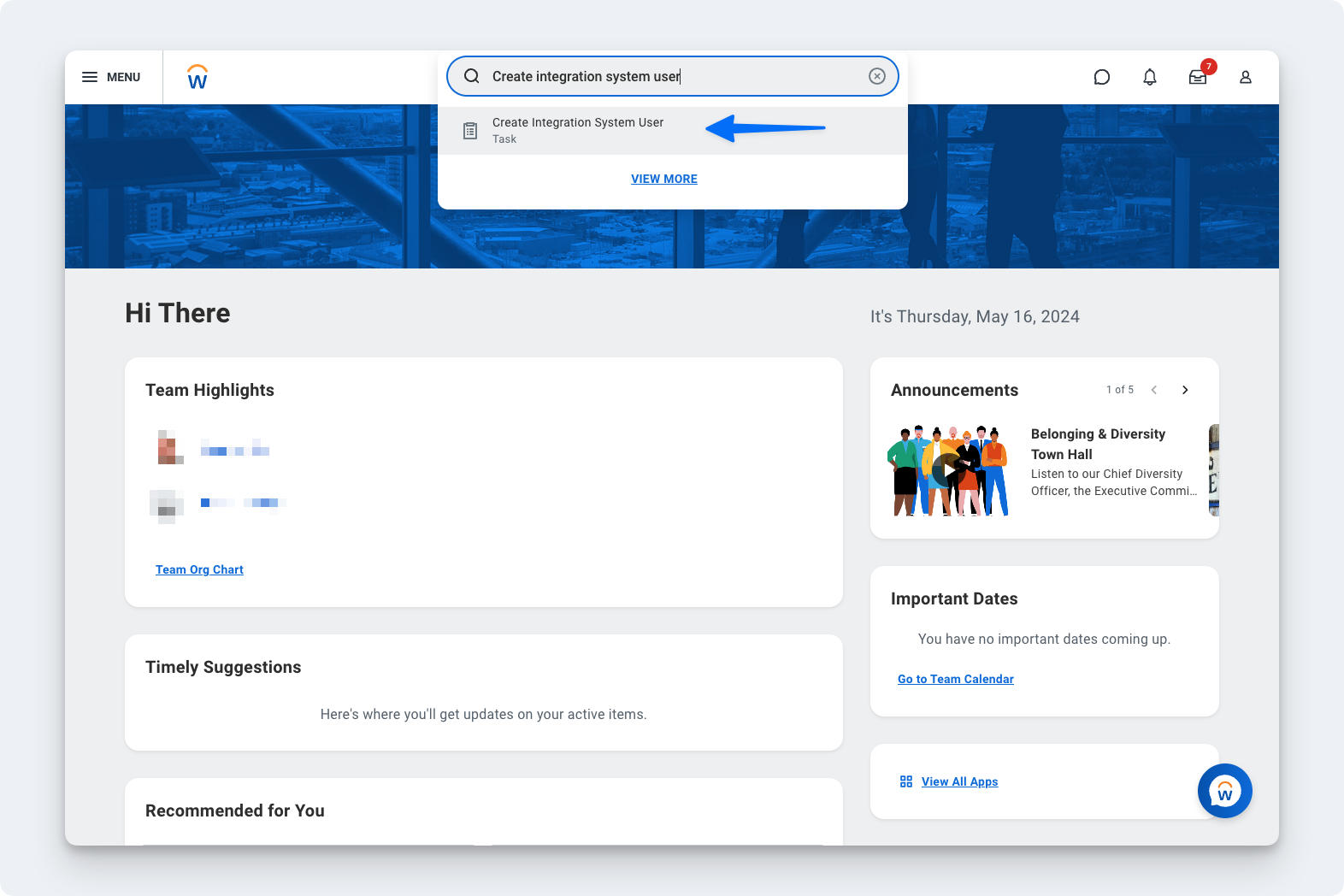
In your Workday portal, log into the Workday tenant
In the Search field, type Create Integration System User
Select the Create Integration System User task
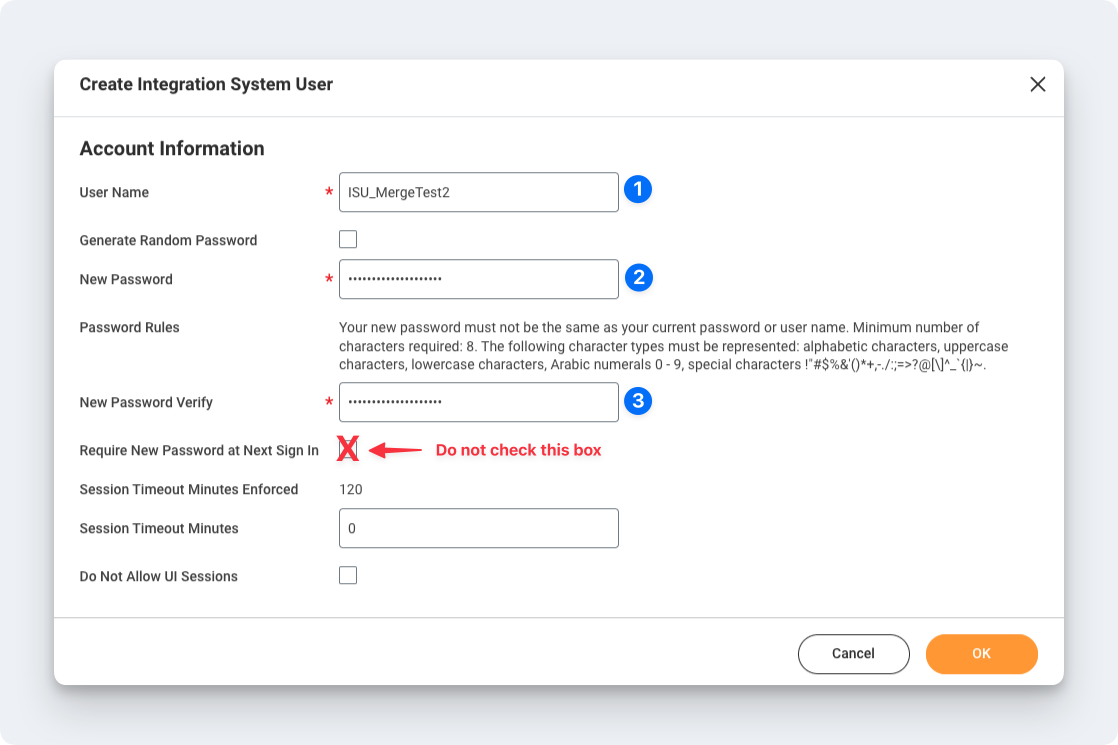
On the Create Integration System User page, in the Account Information section, enter a user name, and enter and confirm a password
Important: "&", "", or ">" characters cannot be included in the passwordClick OK
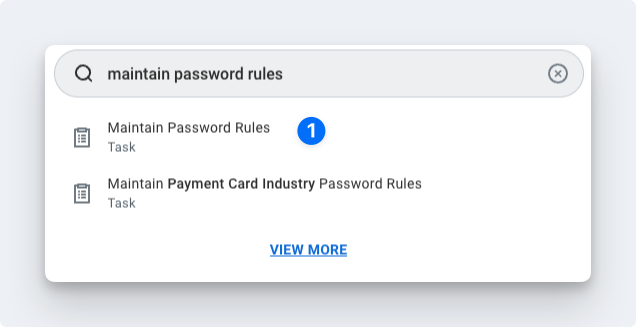
To ensure the password doesn't expire, you'll want to add this new user to the list of System Users. To do this, search for the Maintain Password Rules task.
Add the ISU to the System Users exempt from password expiration field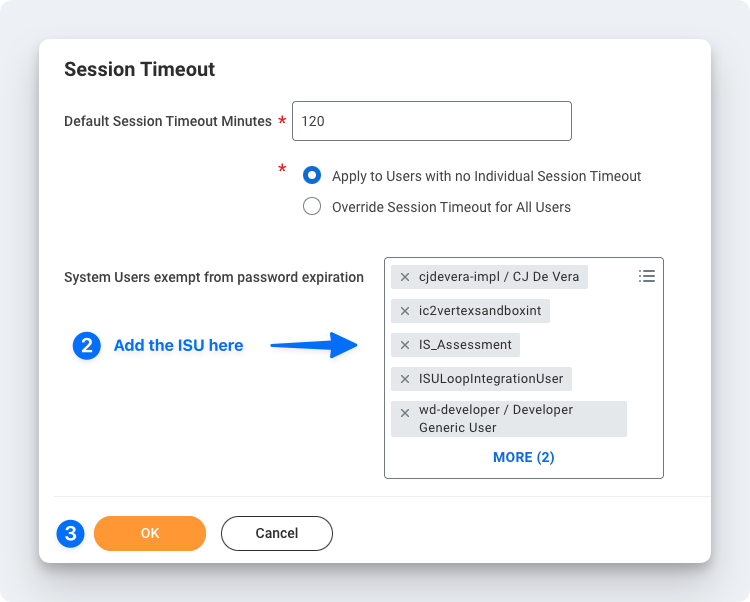
Enter the Integration System User name in the linking flow
Enter the Integration System User password in the linking flow
Step 2: Create a Security Group and assign an Integration System User
In the Search field, type Create Security Group
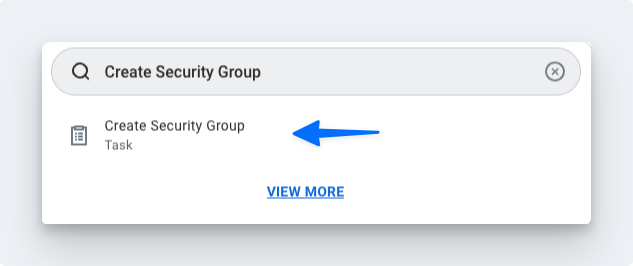
Select the Create Security Group task.On the Create Security Group page, select Integration System Security Group (Unconstrained) from the Type of Tenanted Security Group pull-down menu.
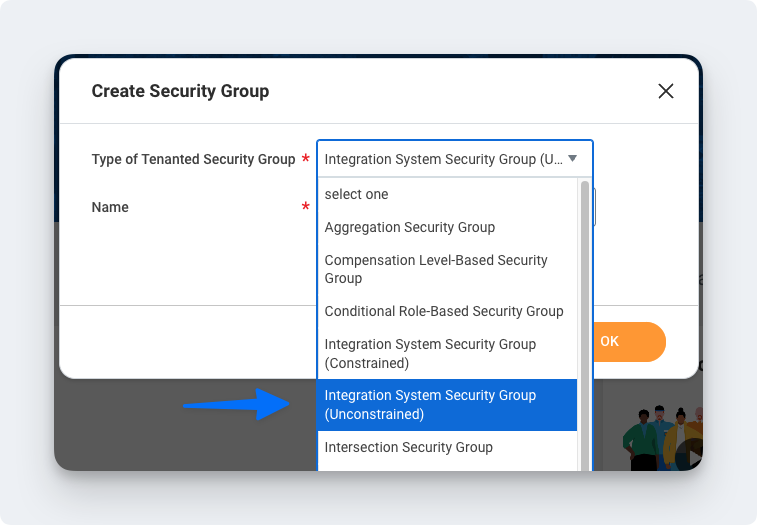
In the Name field, enter a name
Click OK
On the Edit Integration System Security Group (Unconstrained) page, in the Integration System Users field, enter the same name you entered when creating the ISU in the first section
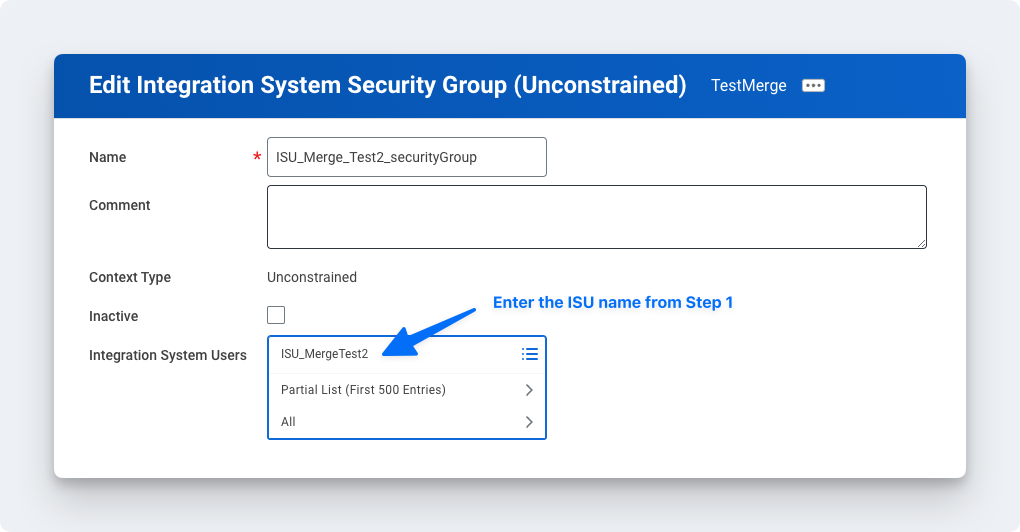
Click OK
Step 3: Configure domain security policy permissions
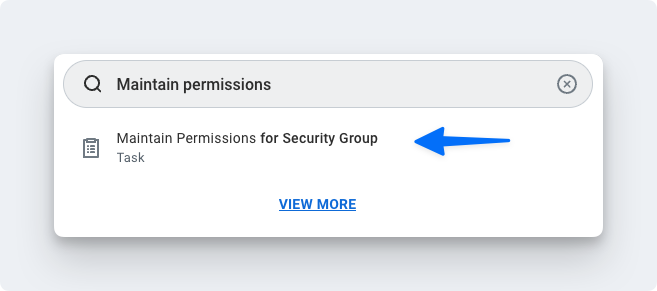
In the Search field, type Maintain Permissions for Security Group
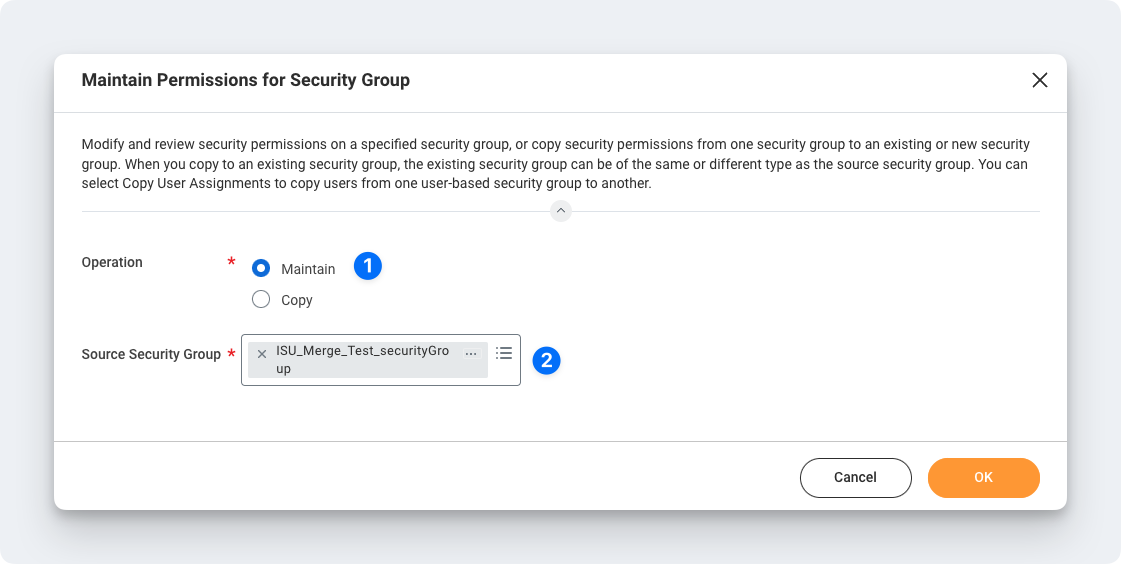
Make sure the Operation is Maintain, and the Source Security Group is the same as the security group that was assigned in Step 2
On the next screen, add the corresponding Domain Security Policies depending on your use case:
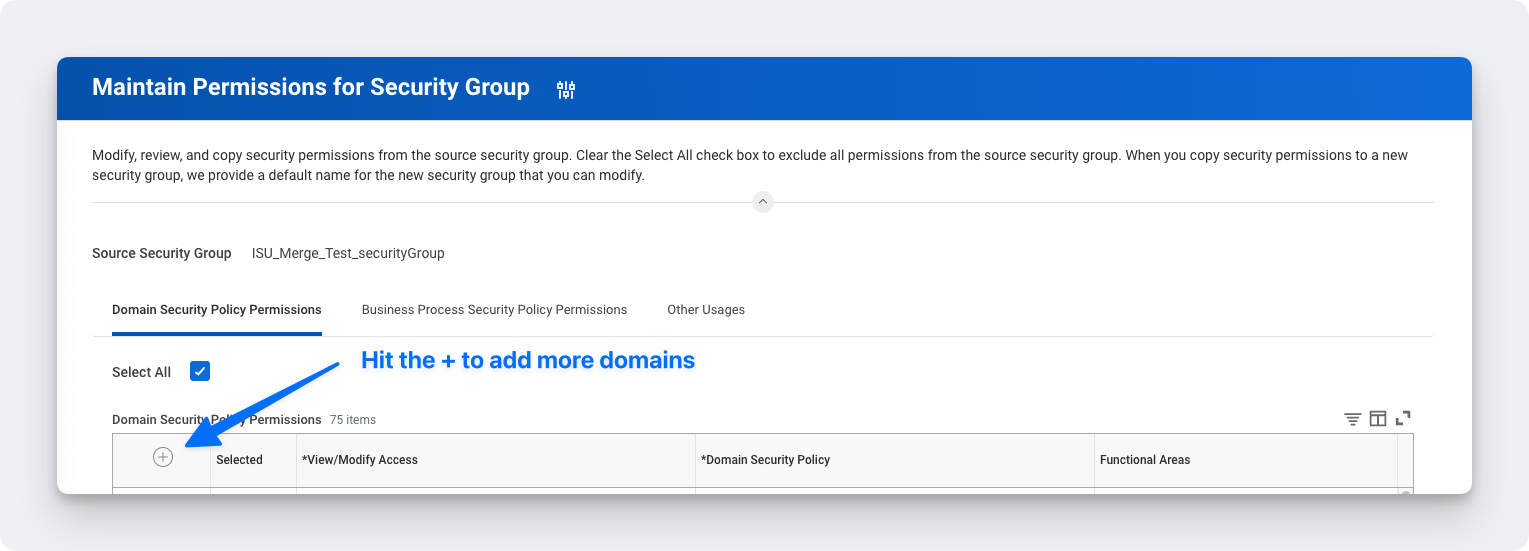
If you are connecting to Workday HRIS:
Follow our HRIS Permissions guide
If you are connecting to Workday ATS (Recruiting):
Follow our ATS (Recruiting) Permissions guide
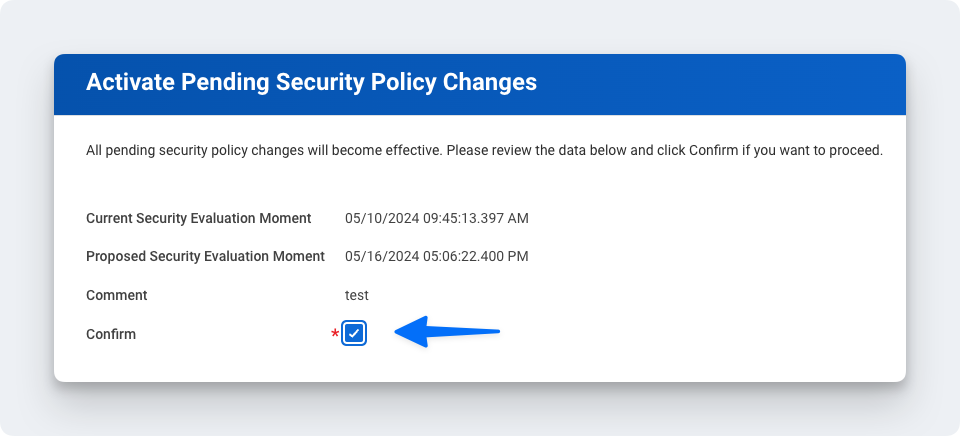
Step 4: Activate security policy changes
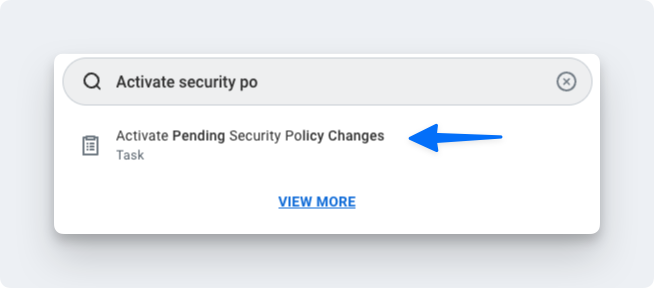
In the search bar, type "Activate Pending Security Policy Changes" to view a summary of the changes in the security policy that needs to be approved
Add any relevant comments on the window that pops up
Confirm the changes in order to accept the changes that are being made and hit OK
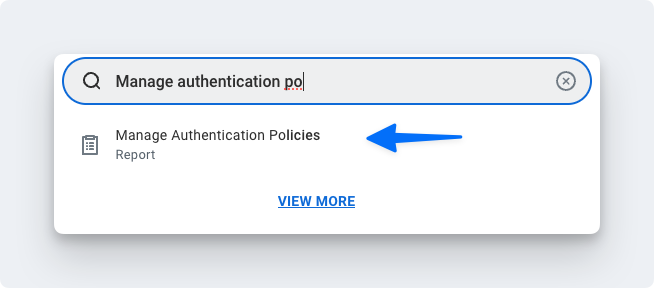
Step 5: Validate the authentication policy is sufficient
Search for Manage Authentication Policies
Click Edit on the authentication policy row
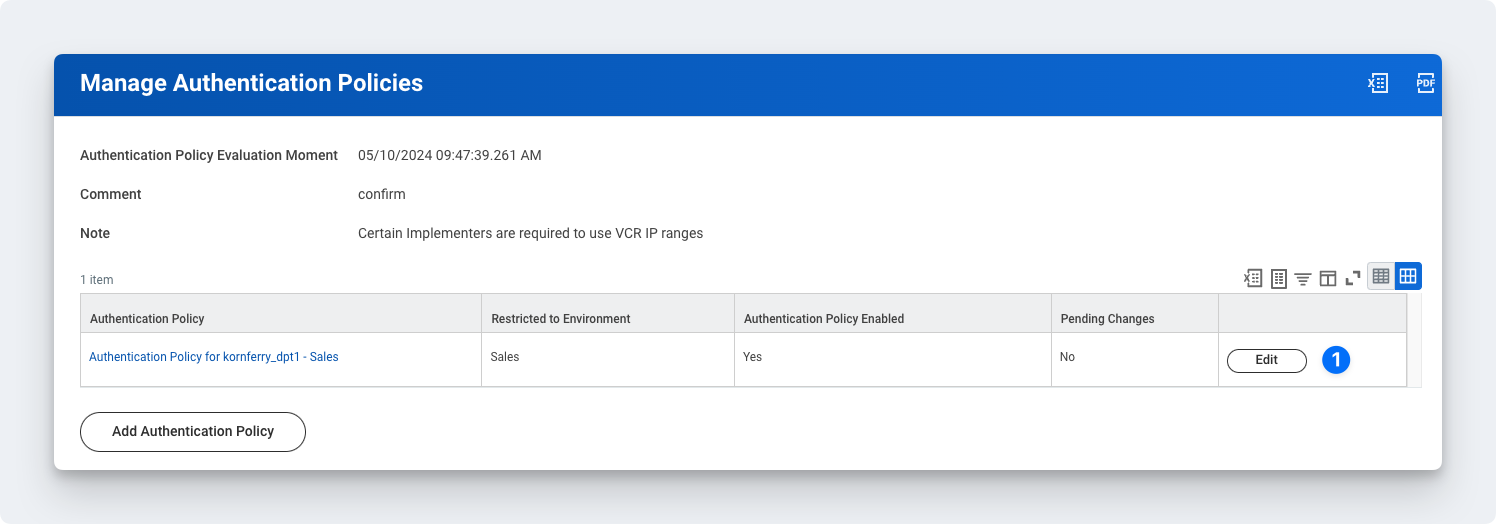
Create an Authentication Rule
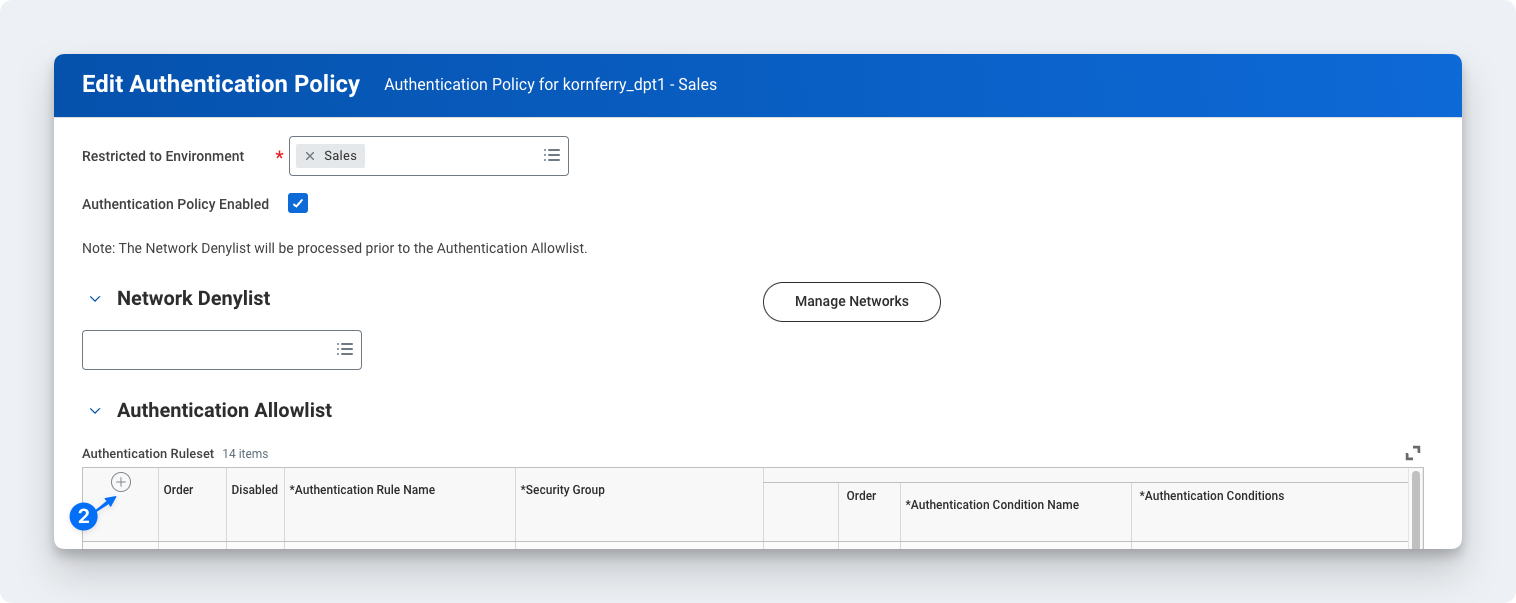
Enter a name, add the Security Group, and ensure Allowed Authentication Types is set to Specific User Name Password or Any
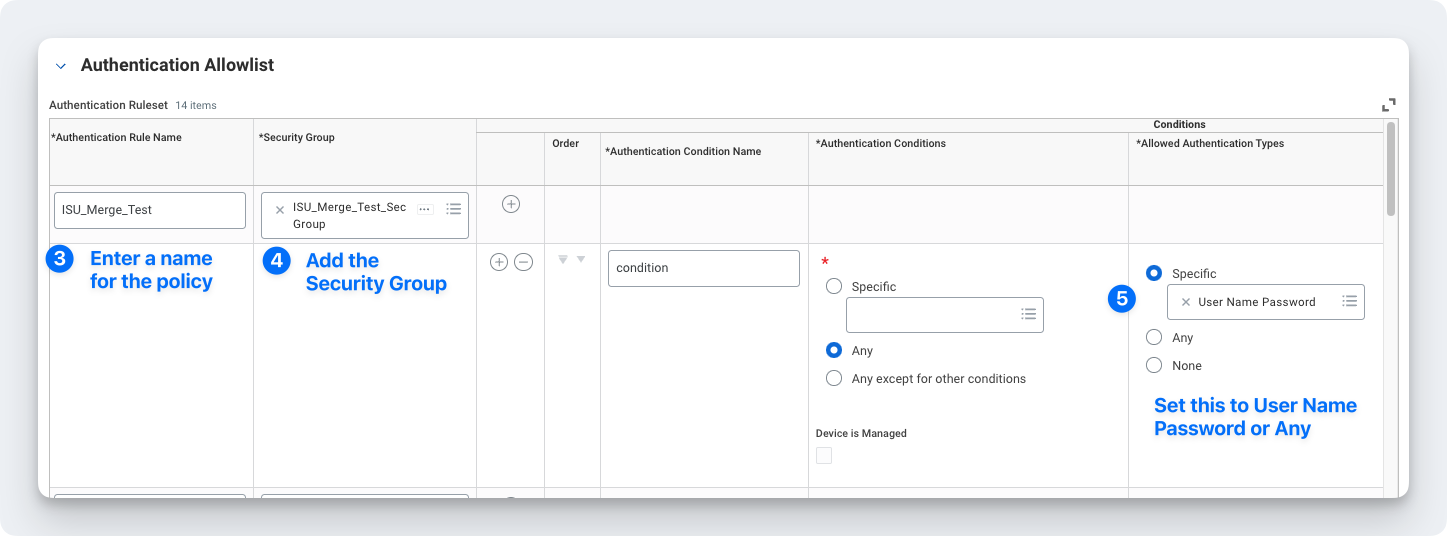
Note: You don't have to create a new Authentication Rule if you already have an existing one set to User Name Password or Any. You can add the ISU you created to that rule instead.
You will need to create a new rule if SAML is the only Authentication Rule you see for "Allowed Authentication Types."
Step 6: Activate all pending authentication policy changes
In the search bar type, activate all pending authentication policy changes
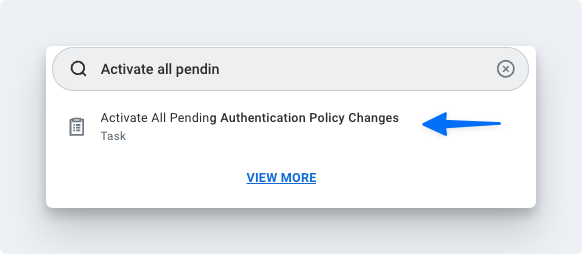
Proceed to the next screen and confirm the changes. This will save the Authentication Policy that was just created or edited
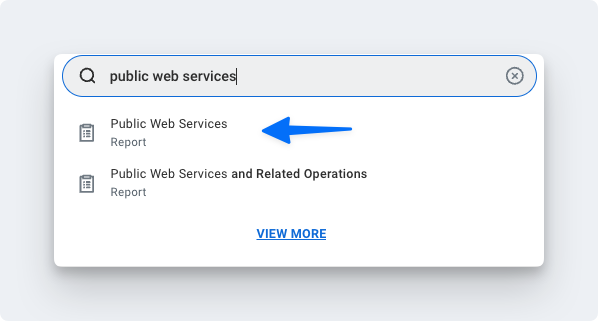
Step 7: Obtain the web services endpoint URL
Search in Workday for Public Web Services
Find Human Resources (Public) if you are connecting Workday HRIS. Find Recruiting if you are connecting Workday ATS.
Click the three dots to access the menu. Click Web Services > View WSDL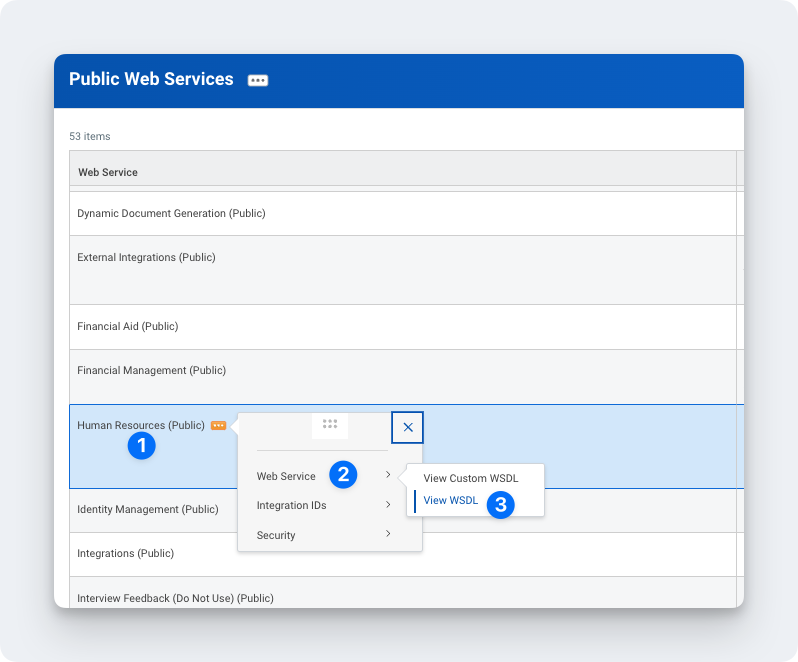
Navigate to the bottom of the page that opens (it may take a few seconds to load)
Copy the full URL provided under Human_ResourcesService (Workday HRIS) or RecruitingService (Workday ATS). The URL will have a format similar to
https://wd2-impl-services1.workday.com/ccx/service/acme/Human_Resources/v43.0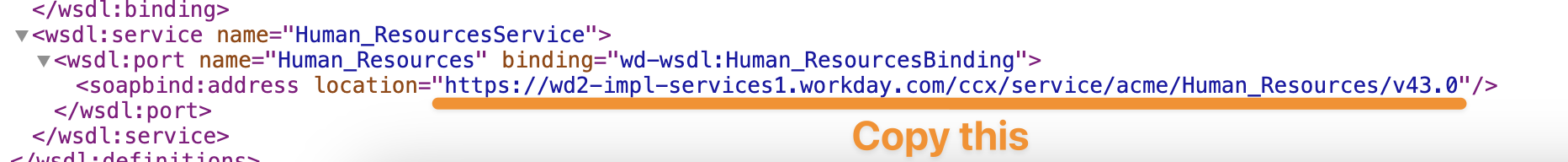
Enter the Web Services Endpoint URL into the linking flow
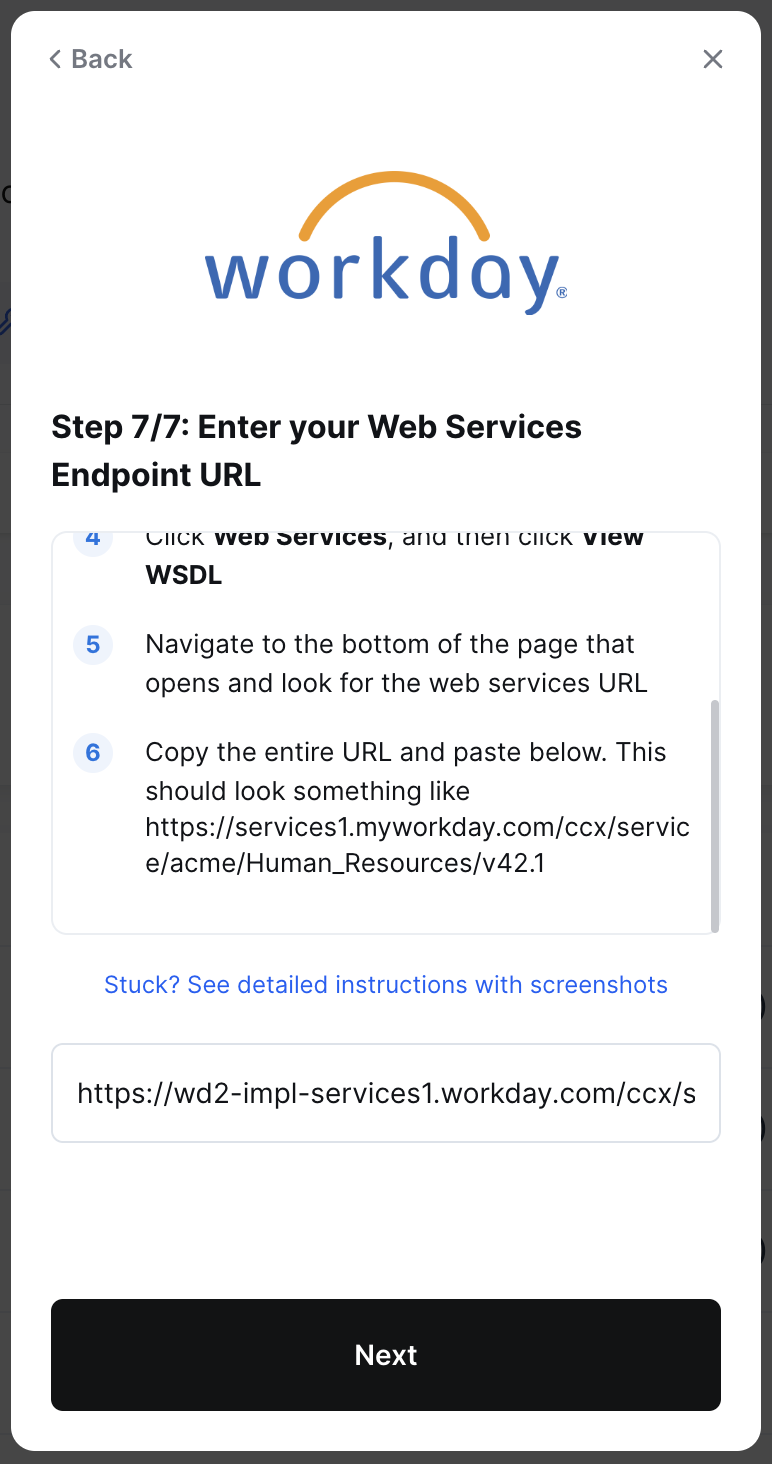
Click Submit
Important Notes
Implementation/sandbox tenant Workday accounts will result in slower syncs, as fewer resources are dedicated to the tenant
In order to increase resourcing for API limits for your Workday tenant, please reach out to Workday Support or your Workday Customer Account Manager.
You can submit a request to Workday Support through the Workday Community support portal