Setting Up ServiceNow Scopes and Roles for Non-Admin Integrations
Last updated: April 2, 2026
This guide explains the minimum roles and Access Control Lists (ACLs) a user needs in ServiceNow to allow your integration (such as Merge) to read and write data through the ServiceNow REST API.
Using these scoped permissions ensures least-privilege access while maintaining full compatibility with core ITSM and CSM functionality.
Overview
ServiceNow uses roles and ACLs to control who can read, create, and update data.
By default, only admins can query system and Customer Service Management (CSM) tables. To integrate using a non-admin user, you must explicitly grant table-level permissions for the data your integration will access.
Create a Custom Role
Navigate to All → User Administration → Roles → New
Fill out:
Name/Suffix:
integration_role(or any custom name)Description:
Custom role for non-admin API access
Click Save
You’ll see a generated name like:
x_<instance_prefix>_integration_roleThis role will be used in all ACLs and assigned to your integration user.
Create a Non-Admin Integration User
If the integration user doesn’t exist yet:
Go to All → User Administration → Users → New
Fill out:
User ID:
integration_userActive: ✅
(Optional) Web service access only: enables API-only access
(Optional) First name / Last name / Email: recommended
Click Set Password to assign a local password (required for Basic Auth)
Make sure Password needs reset is unchecked
Click Save
Assign the Role to the User
Open your integration user record
Scroll to Roles → Edit
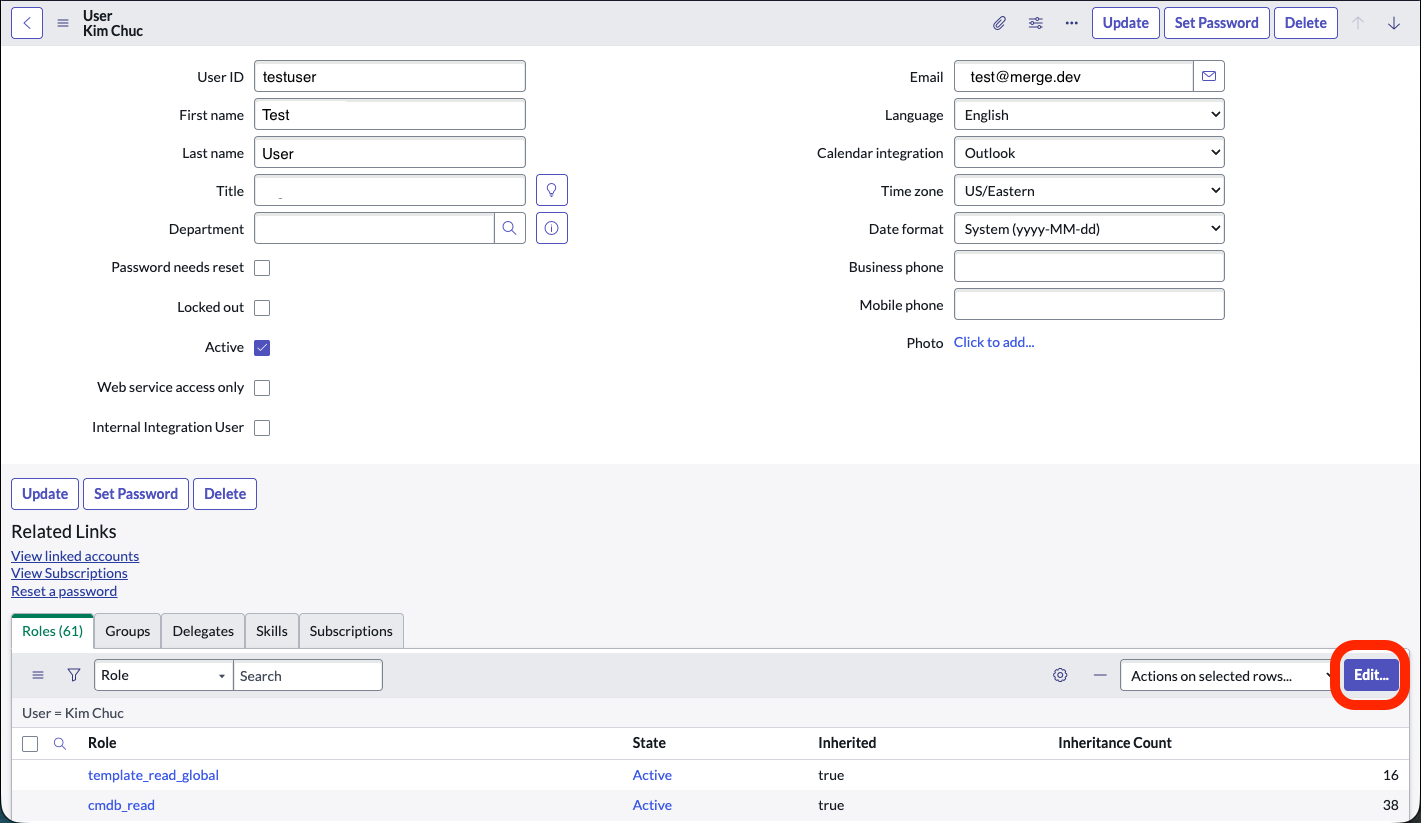
Search for and add the role you created:
x_<instance_prefix>_integration_role
(Optional) If your integration also needs ITSM data like Incidents or Tasks, add:
itilsnc_platform_rest_api_access
Click Save.
Your user now has a scoped role that will be used for ACL permissions.
Create Custom ACLs (Access Control Rules)
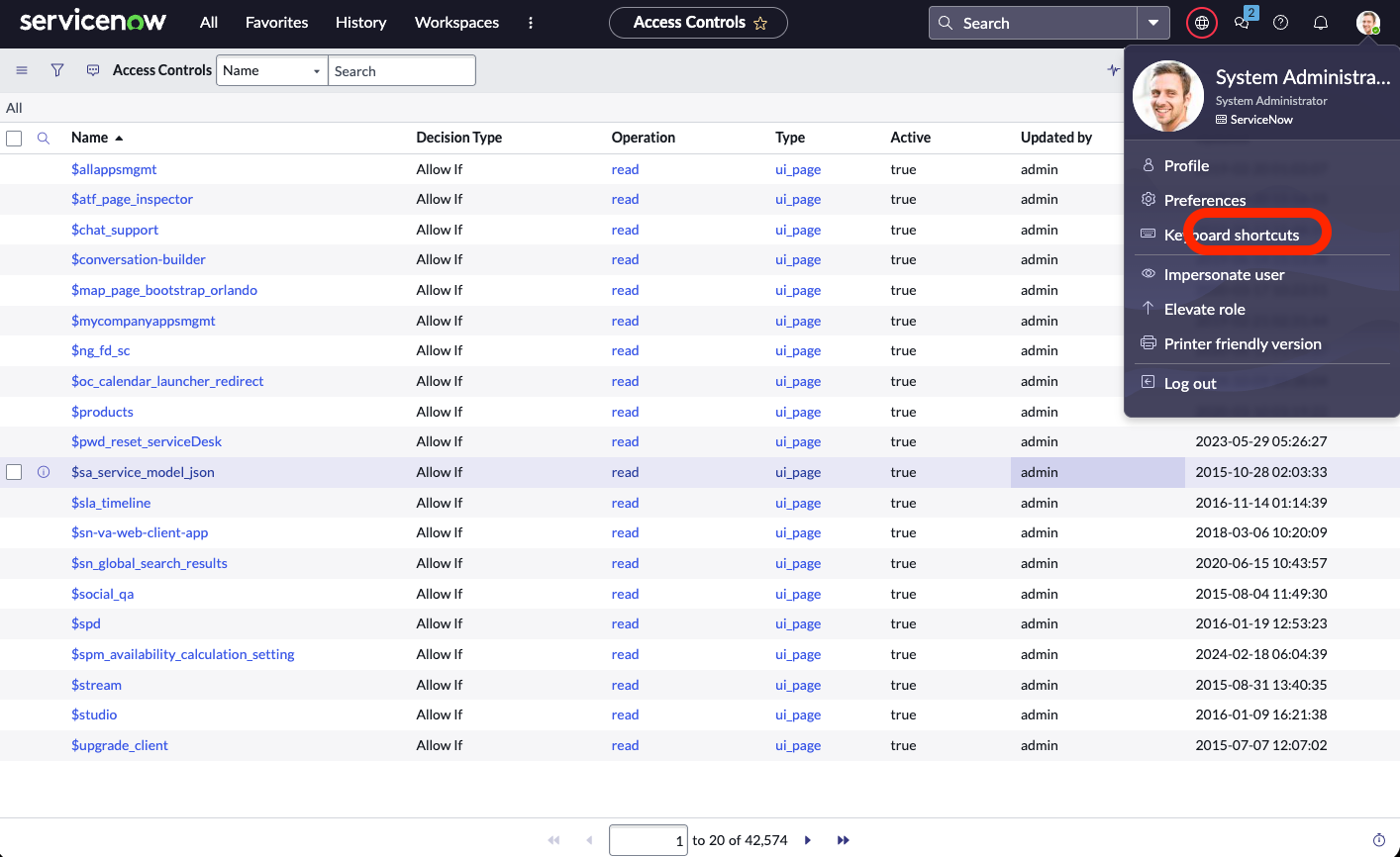
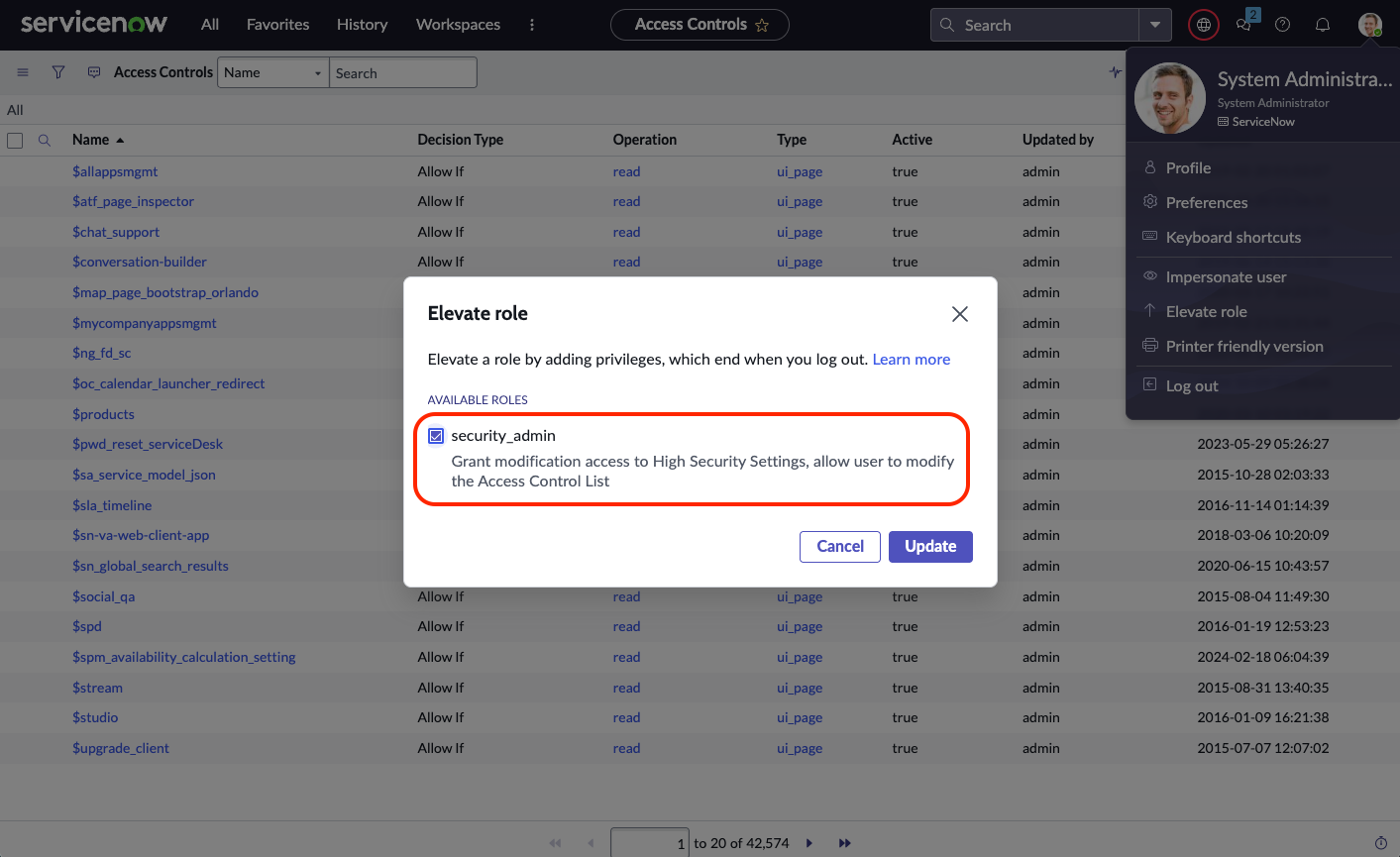
Before creating a Custom ACL, make sure your role is allowed to add Custom ACLs. This can be manually done by Elevating role and enabling the security_admin role for the user:
ServiceNow ACLs define which roles can perform actions on which tables or fields.
You must create one ACL per table (or field) and per operation type (read, write, create).
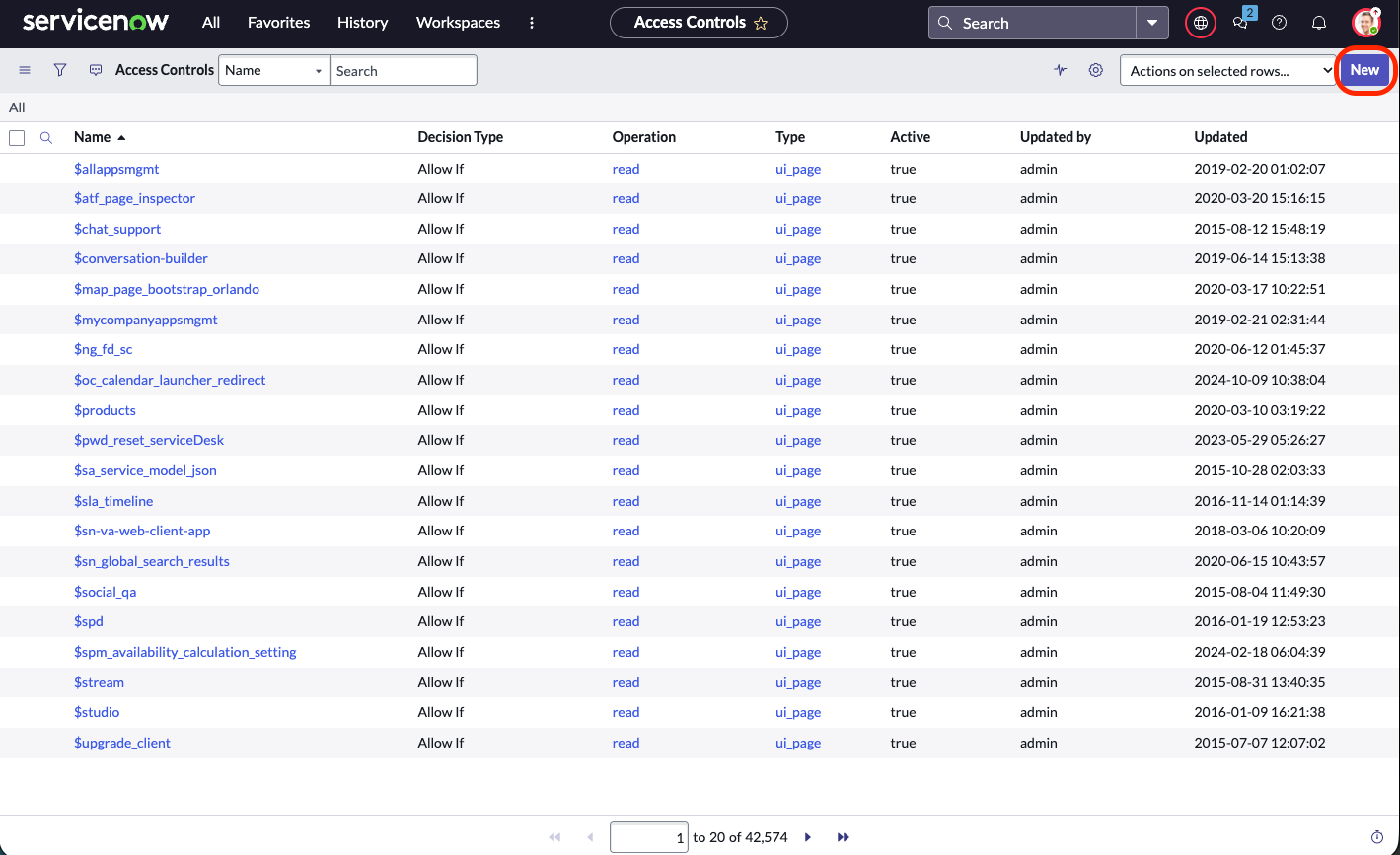
Go to:
All → System Security → Access Control (ACL) → New
Fill out these fields:
Field | Value |
Type |
|
Operation |
|
Name | Table name (e.g. |
Requires role | Your custom role (e.g. |
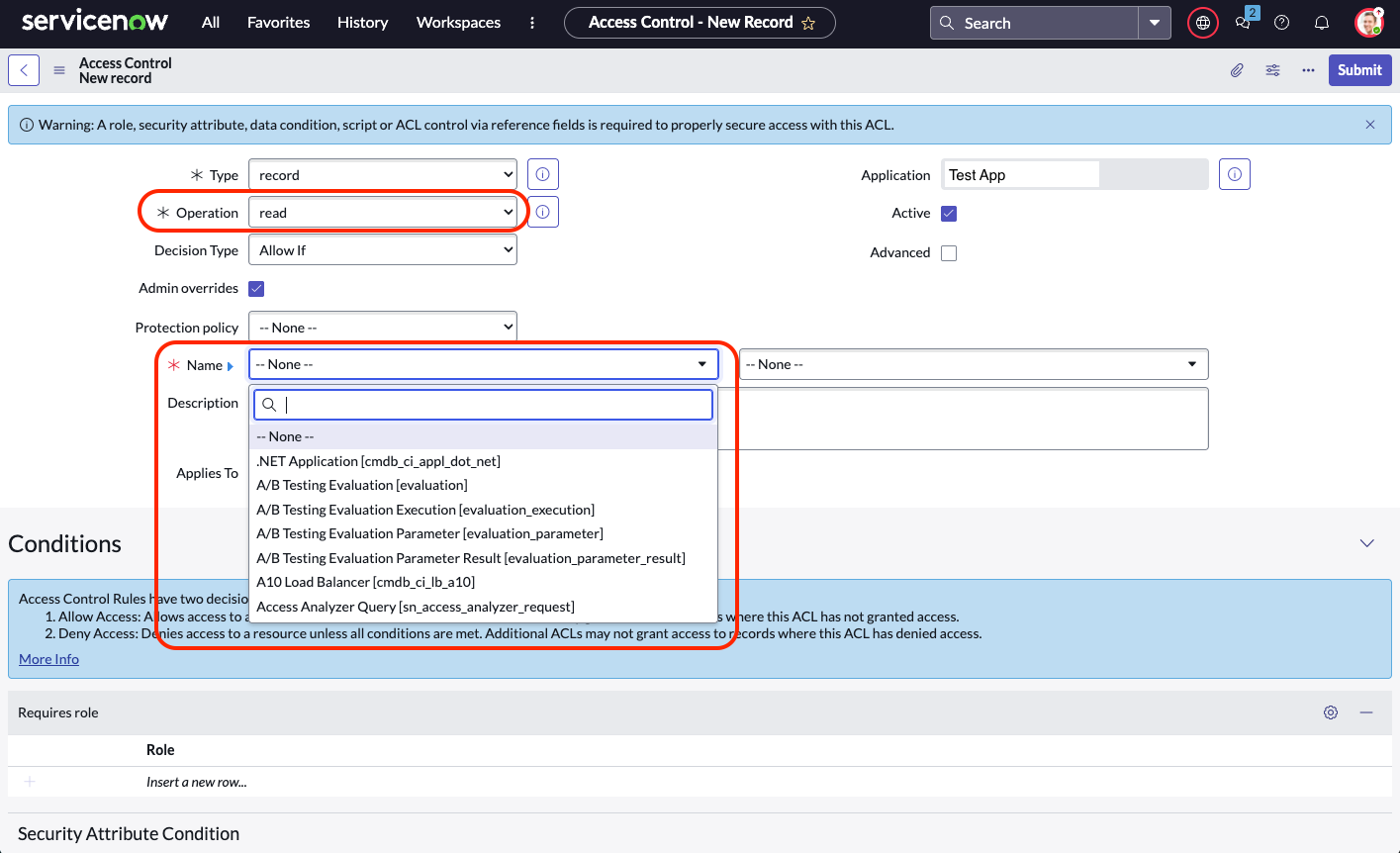
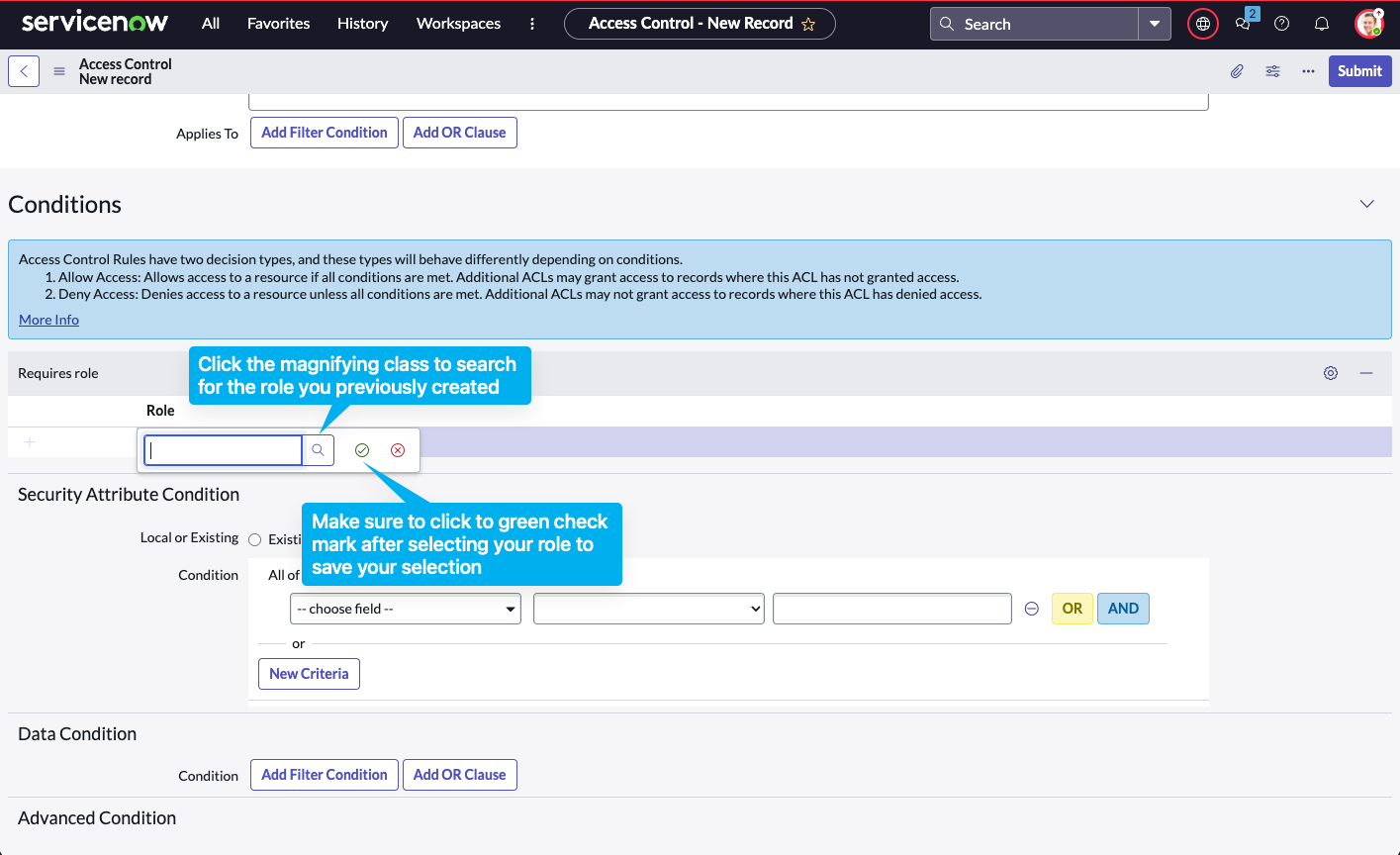
Click Submit.
Repeat this for every table you need access to.
Add ACLs for Each Required Scope
Each ServiceNow “scope” (table) must have its own ACL.
Below is a complete list of common API endpoints, what they do, and what role or ACL grants access.
Core systems table
Table | Required role | ACL Description |
| Custom ACL for | User records (needed for user lookups like |
|
| Field and schema metadata |
|
| Dropdown / picklist values |
| Custom ACL for | Database table metadata |
|
| File attachments on records |
|
| Comments and work notes |
Customer service management
Table | Required role | ACL description |
|
| Customer/consumer records |
|
| Customer Service cases |
ITSM and Task management
Table | Required role | ACL description |
|
| Incident, problem, and request records |
Additional Scopes to Include in Custom ACLs
These system tables are frequently queried by integrations. Add read ACLs for your custom role to prevent 403 errors.
Table | What it represents | Why it's needed | Grants access to |
| User directory | Needed for user lookups |
|
| Field definitions | Needed for metadata and schema introspection |
|
| Choice-list values | Needed for dropdown and picklist labels |
|
| Table registry | Needed to enumerate available tables |
|
| File attachments | Needed to read or upload attachments |
|
| Comments / work notes | Needed to read or post ticket comments |
|
| Customer/consumer records | Needed to link CSM cases to users |
|
User and Role Data
To minimize privilege, use your custom integration role with targeted read ACLs for user-related tables.
Table | Purpose | Required role / ACL |
| User records |
|
| Role assignments |
|
| User groups (Teams) |
|
| Group memberships |
|
| Table metadata | Custom read ACL (admin-only by default) |
Tickets (Tasks, Incidents, Requests, Problems, Cases)
The itil role grants full CRUD access to ITSM “task” tables, including incidents, problems, and catalog tasks.
If integrating with CSM, add sn_customerservice_agent.
Table | Purpose | Required role / ACL |
| Base task table |
|
| Incident management |
|
| Problem management |
|
| Service catalog requests |
|
| Service catalog tasks |
|
| CSM cases |
|
Comments (Journal Fields)
Journal fields (comments, work notes) inherit ACLs from their parent record.
If your integration can read/write incidents or tasks, it can usually access related journal fields automatically.
Table | Purpose | Required role / ACL |
| Comments, work notes, and activity logs |
|
Attachments
Attachments inherit permissions from their parent record.
Your integration user must have read access to one of the parent tables (e.g., incident, task, sn_customerservice_case).
Table | Purpose | Required role / ACL |
| Attachment metadata |
|
Writing Tickets (POST Access)
To create new tickets via the Table API (POST /api/now/table/<table_name>), your user must have create ACLs or roles granting write access.
Table | Purpose | Required role |
| Create incidents |
|
| Create problems |
|
| Create generic tasks |
|
| Create catalog tasks |
|
| Create service requests |
|
| Create customer cases |
|